
Impossible that you have never been confronted with one of those! Scams, fraudulent attempts, are omnipresent on the Internet. After decrypting the practice of “slamming” in one of our previous articles, find out about “phishing” and the good behaviours to prevent yourself from it.
What is “phishing”?
It is an abuse technique designed to attract victims to a website that is at every point similar to a website they are familiar with. Their purpose? To steal confidential information. How do fraudsters do this?
First, phishers have to create a replica of the website they are trying to divert the traffic from. This duplicate site will be used to trick users into entering their login information. Once the authentication proceeded, the phisher has the freedom to use this data for his own benefit. For example, he can access services by impersonating one of his victims. It may also use confidential information such as bank details.
First of all, the scammer must attract its victims to the pirate site. It is a technique called “social engineering” which means that it is based on a human “failure” rather than a technical one. The hacker simply focuses on the user’s good faith or lack of attention.
How do the scammers convince their victims to visit their pirate site? Several techniques exist, but the most frequent medium used is email. Here are some tips to recognize these fraudulent emails and avoid scams attempts.
“The essence of phishing is to be the closest to the original, never stop at what you see, otherwise you will be fooled.”
4 key tips to guard against phishing attempts!
The sender
1. Never trust the sender!
There is nothing easier than creating or falsifying an email address. Keep in mind that some email clients do not display the entire email address by default but simply the first/last name of the sender. Therefore, a first phase of control could be to check the concordance between the email address and the first/last name displayed.
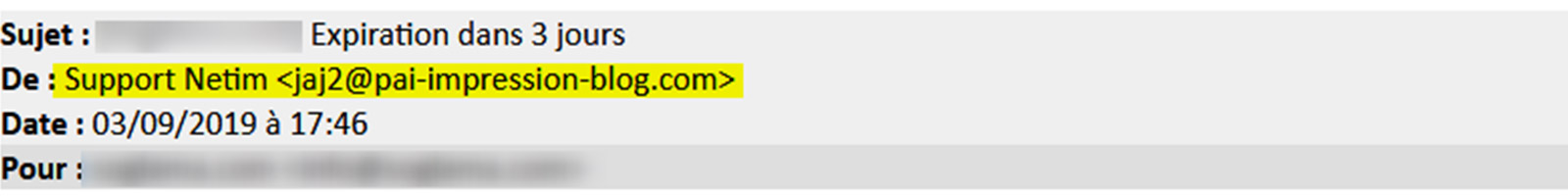
In this example, we note that “Netim Support” is actually an address unrelated to our company.
But the crooks are far from being ignorant in computer sciences. Furthermore, it is such an easy thing to change an email address, that you can’t take it for granted. Mistrust is a necessary thing to keep in mind. You will be amazed by how easy it is to pretend to be someone else on the internet.
The body
2. Never open attached files from an unknown sender.
Warning! An attachment sent by a malicious person can cause huge damage once opened and/or executed. It is therefore strongly discouraged to open any attachment from an unknown or doubtful sender.
3. Don’t be impressed by an alarmist tone!
Never act in a hurry, pirates play with the fears of their potential victims. If a service invites you to act quickly without prior notice, beware! You will always receive several reminders before a deadline.
4. Never email your password
Never give your password in response to an email. Companies are not supposed to store your password, so it cannot be a reliable authentication method.
The external links
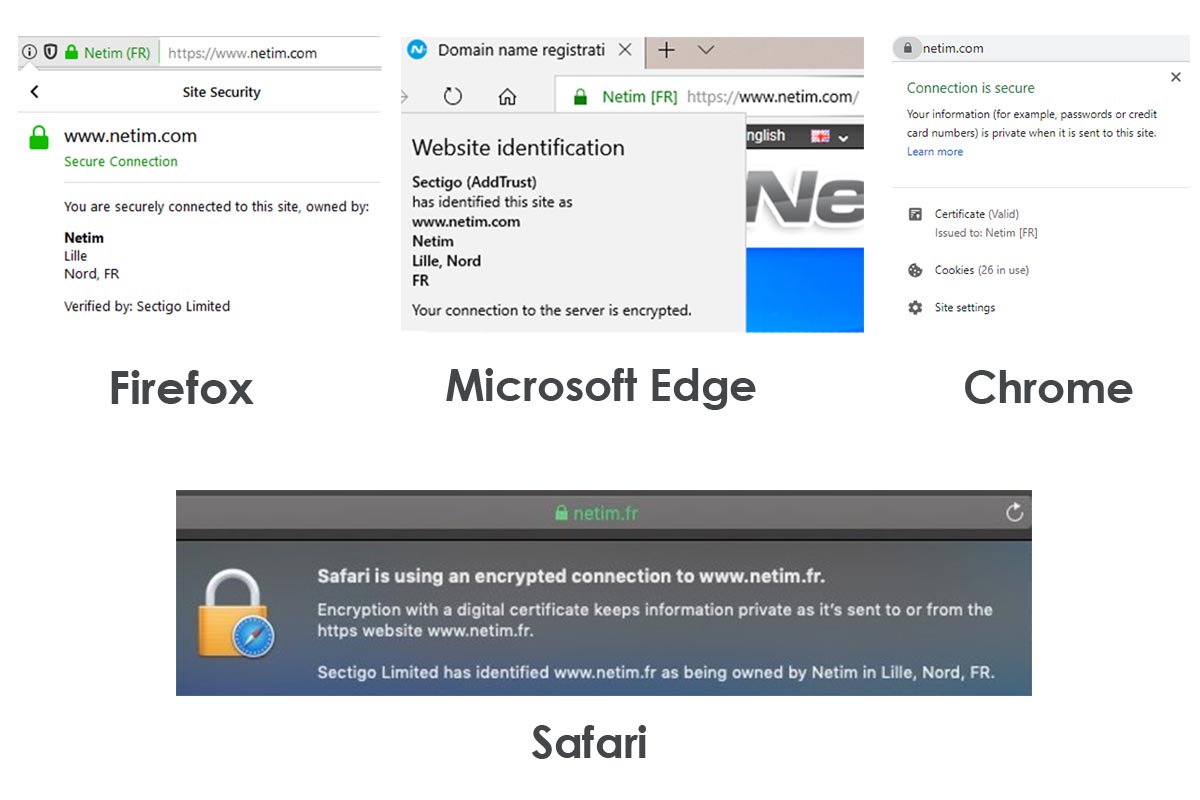
5. Verify the secure connection of hyperlinks
Secure connections are the new standard for any business. There are different kinds of secure connections, allowing different degrees of security: DV (Domain Validation), EV (Extended Validation). Some of these standards are more or less reliable, such as the DV certificate that does not need any certification to be obtained. Therefore, they are not always a guarantee of authenticity.
Nevertheless, a lack of secure connection is in most cases, synonymous with danger.
If an email prompts you to connect directly to a payment (even secure), always prefer to log in independently to your customer area rather than follow the link in the email’s body.
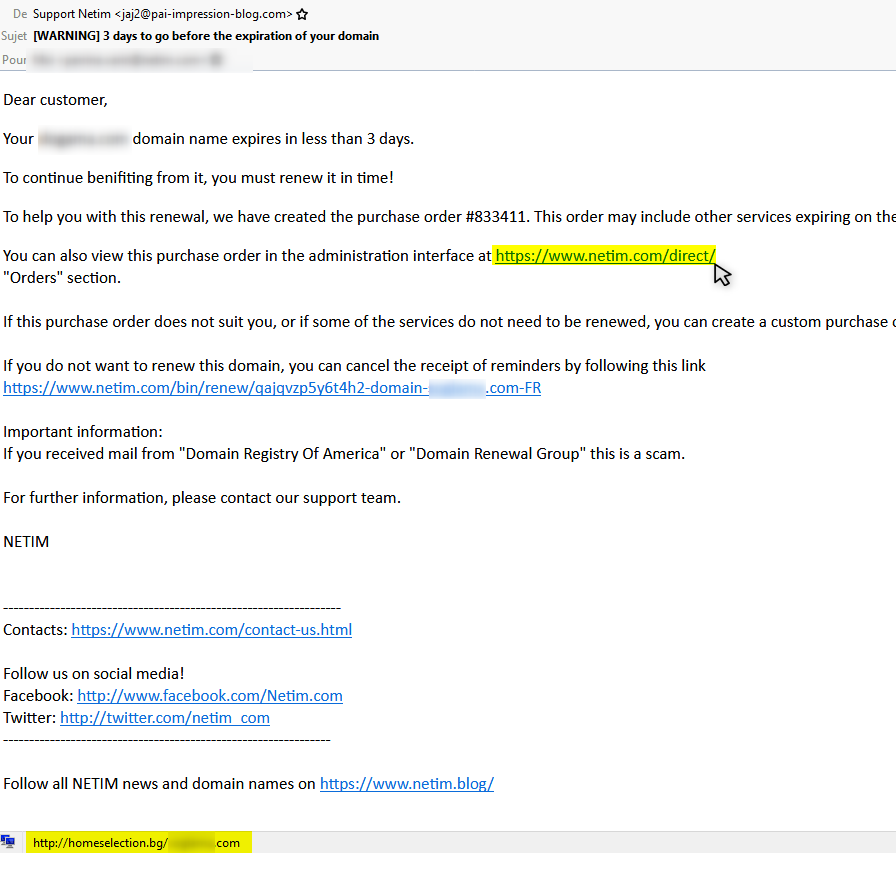
6. Verify that the hyperlinks in the mail match the Urls they refer to.
When a suspicious email invites you to click on a link to retrieve your personal information, it is more than advisable to check the exact address of the site to which it refers. How can I do it safely? Simply pass the mouse over the link (without clicking), you will see at the bottom of the page the address to which you will be going.
7. Beware of the IDNs!
IDN stands for Internationalized Domain Name. So this refers to special characters: accented letters, non-Latin characters etc. What does this have to do with phishing? These characters make it possible to visually falsify a URL by means of homogenlyphs (typographical character seeming similar to another).
For example, https://www.аррӏе.com/ is very similar to the apple site. This is actually a domain composed of IDN and gives once transcribed: https://www.xn-80ak6aa92e.com/. Rather impressive, isn’t it?
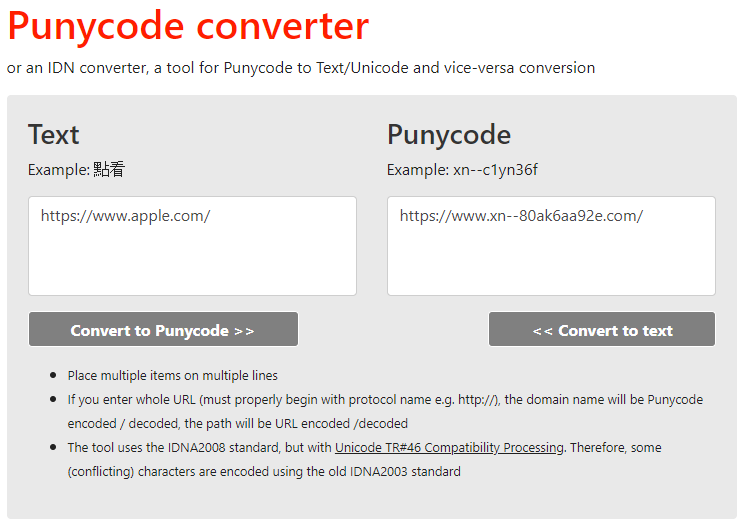
Another well-known example is that of the company Air France which saw its site be diverted by the use of special characters such as the ą. The point below the “a” disappears once the link is active.
8. Watch out for shortened URLs!
One way to fool the user is also to use shortened URLs like bit.ly, goo.gl etc. If you have any doubt as to the veracity of an email you received do not follow these shortened links.
In short!
- The sender
- The content of the email
- An email asking you to act urgently
- Attachments included in the email
- The links present in the email
- Shortened URLs
- Secure connections and HTTPS presence
- The domain name you see
- Never trust and go manually to the desired site!
To go further …
Many kinds of abuse exist on the Internet and are often complicated to stop them. The best defence against this type of scam is vigilance on the one hand, and information on the other. Many fraudulent practices do not have a precise legal definition, which allows these pirates to continue their actions.
Google has set up a quiz to learn how to fight phishing. One more proof that this type of attack concerns even the biggest web industries! Will you be able to detect phishing attempts? Take the test to learn more.
If you want to know more about the various existing abuses, do not hesitate to consult our article “Beware of “slamming”, a practice of domain name scams!”





